Meet the Agent That Builds Your Operation for You
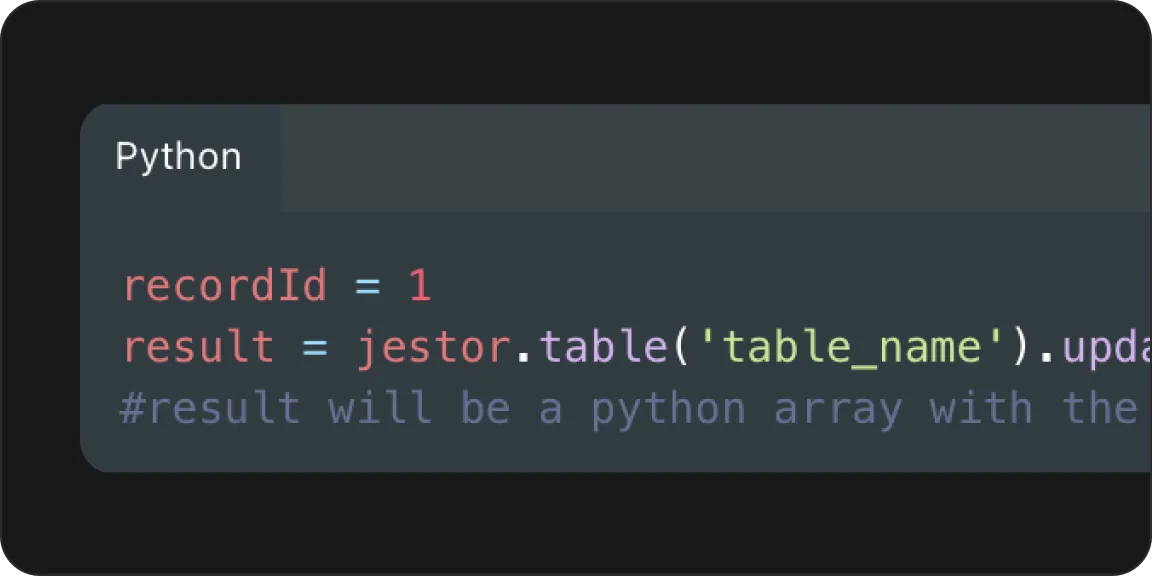
Just describe what you need. Jestor's AI Agent creates apps, tables, and internal tools for your team — instantly, without code, without developers.
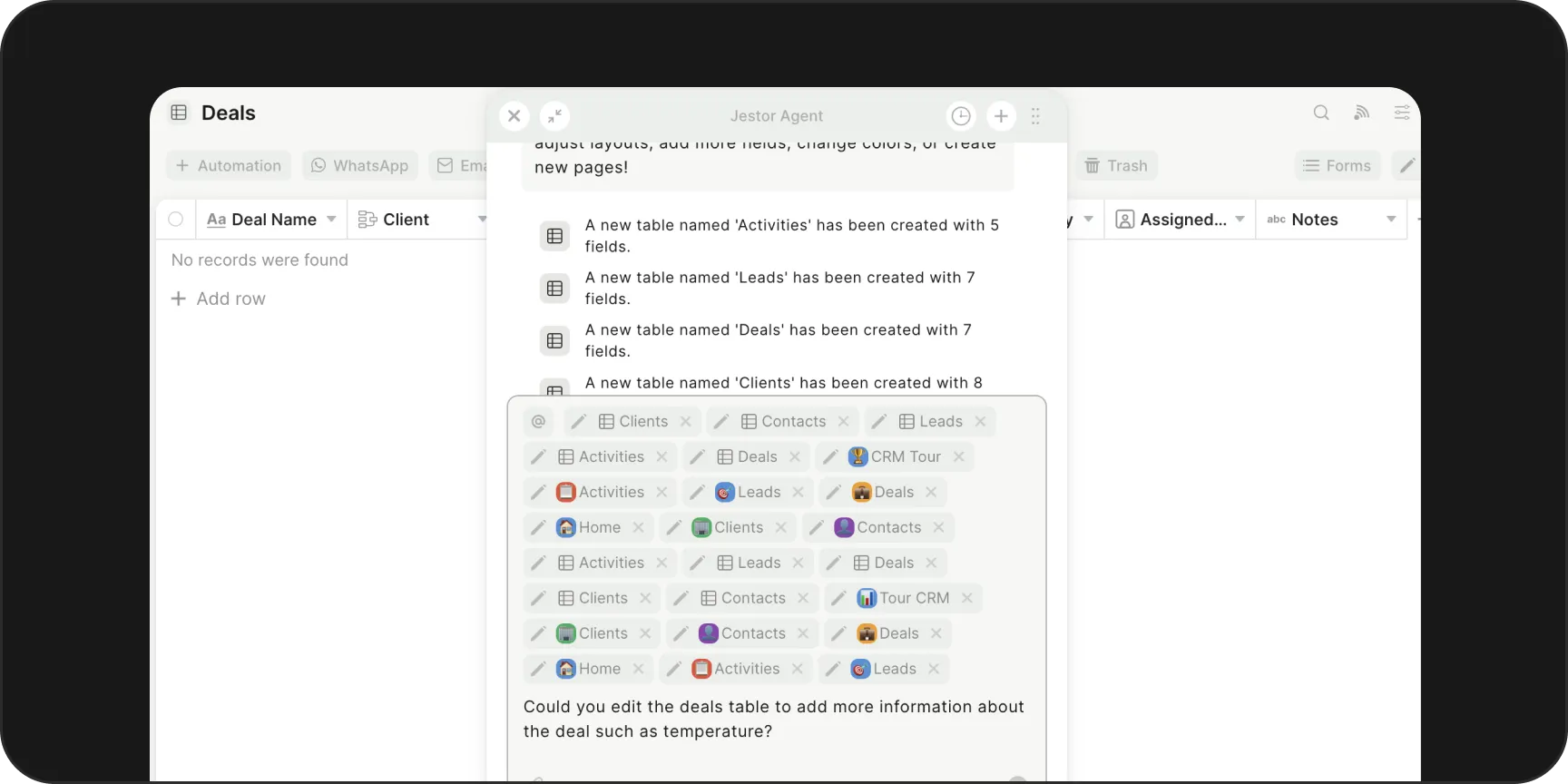
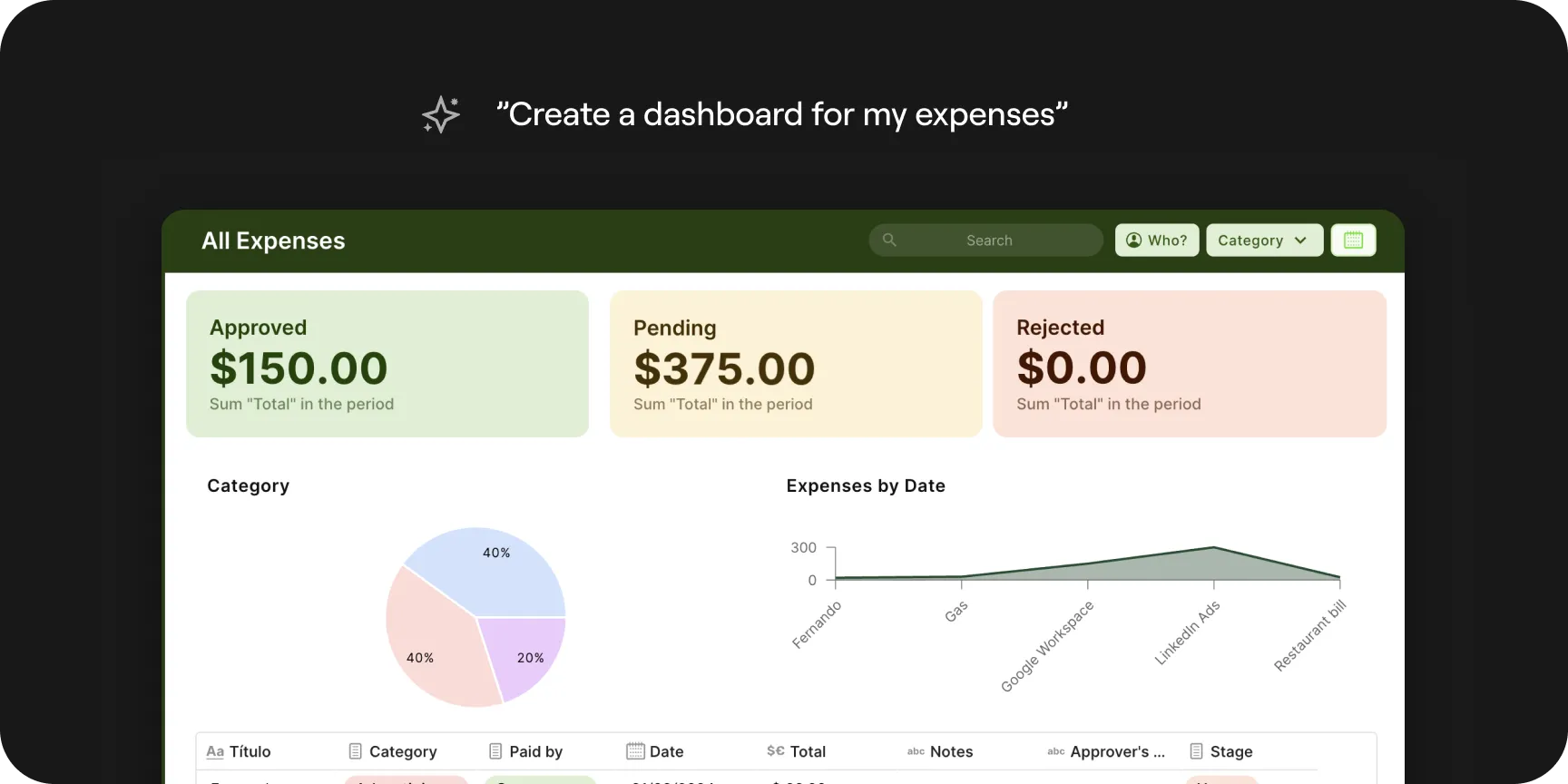
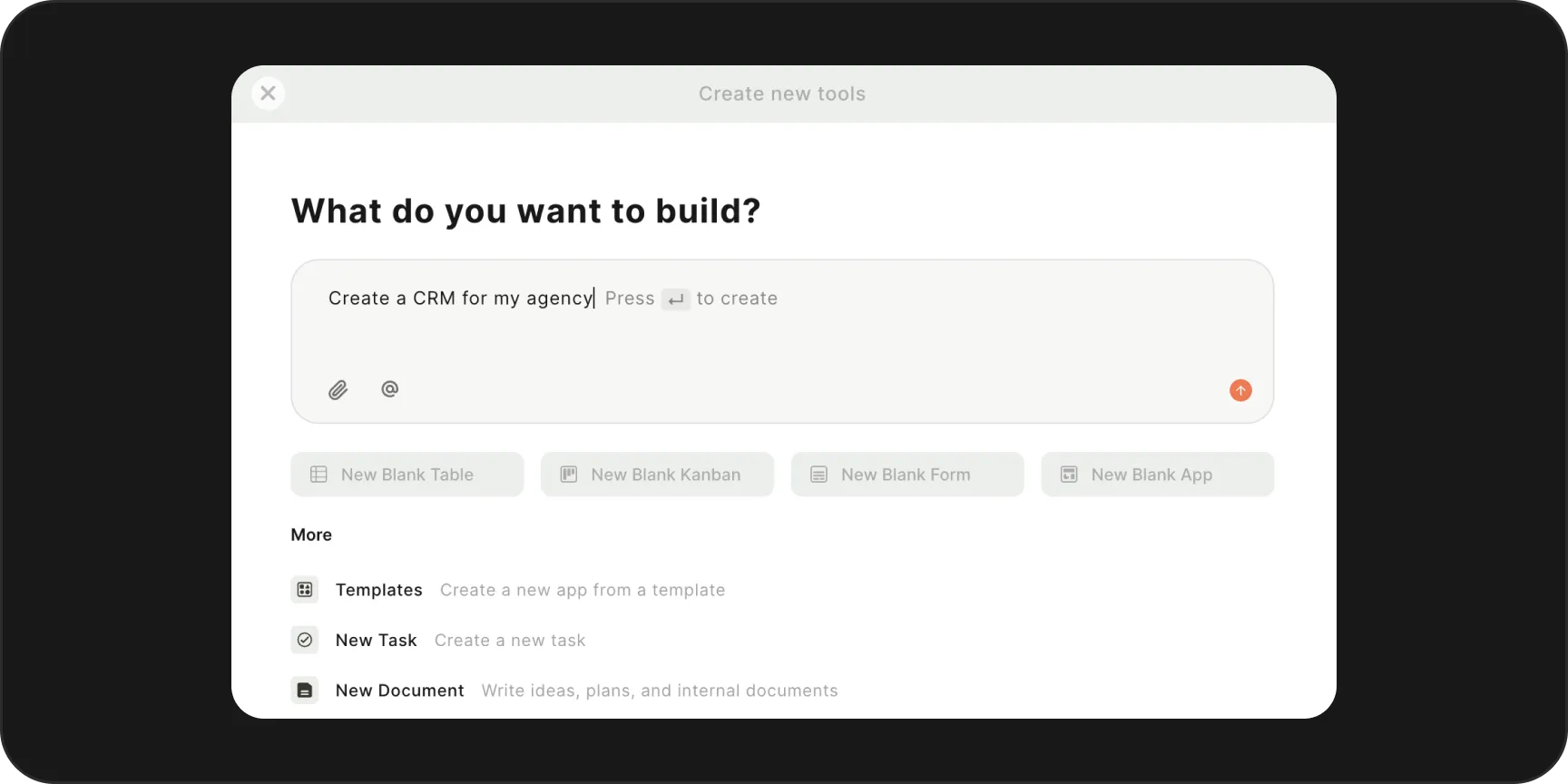
Builder Agent
Create complete apps from a single prompt.
Tell the agent what your process looks like and it builds a fully functional app for you — fields, logic, and layout included.
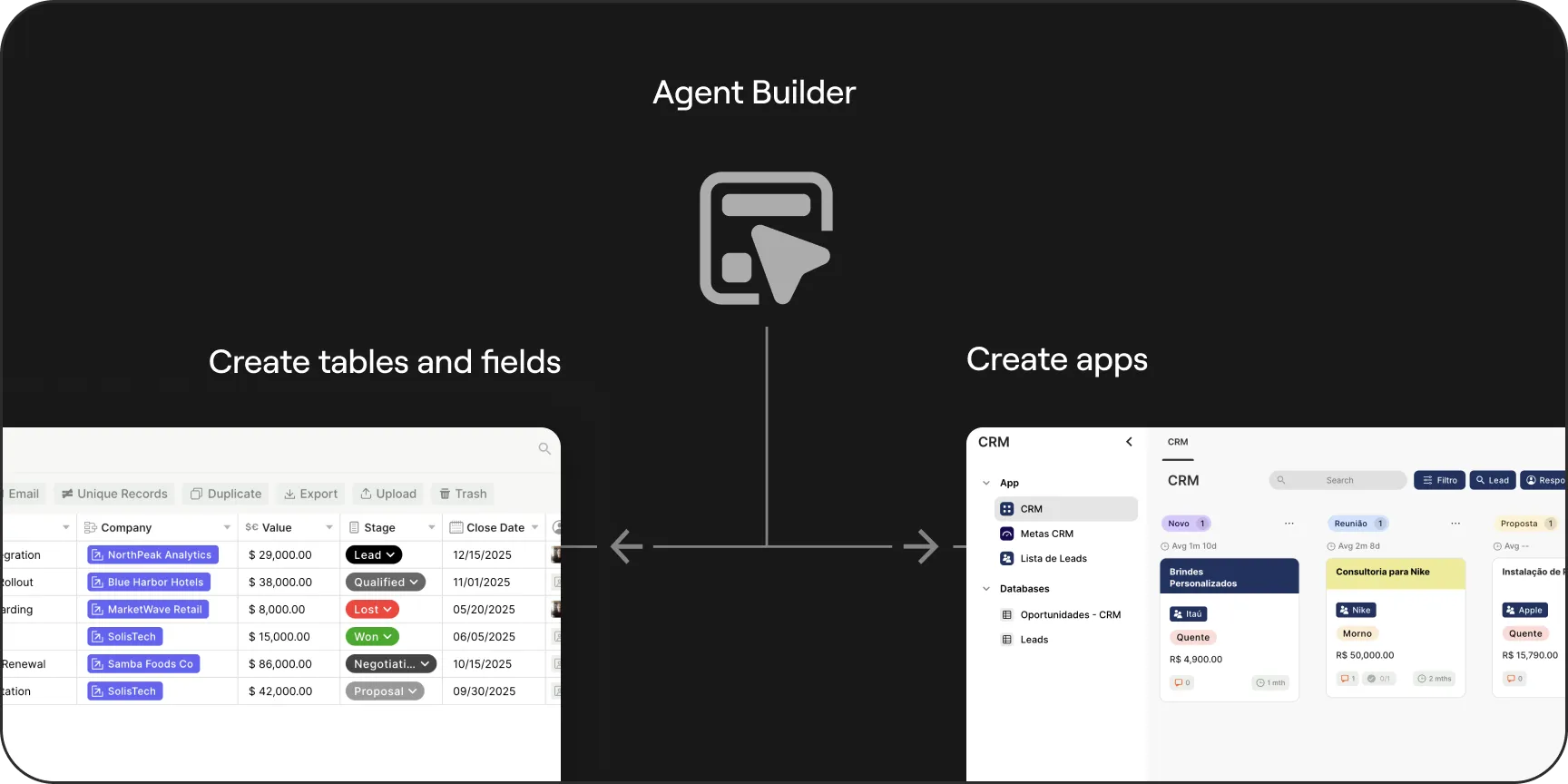
Generate the right tables for your data.
The agent structures your data model from scratch. No manual setup, no guesswork — just organized, ready-to-use tables inside Jestor.
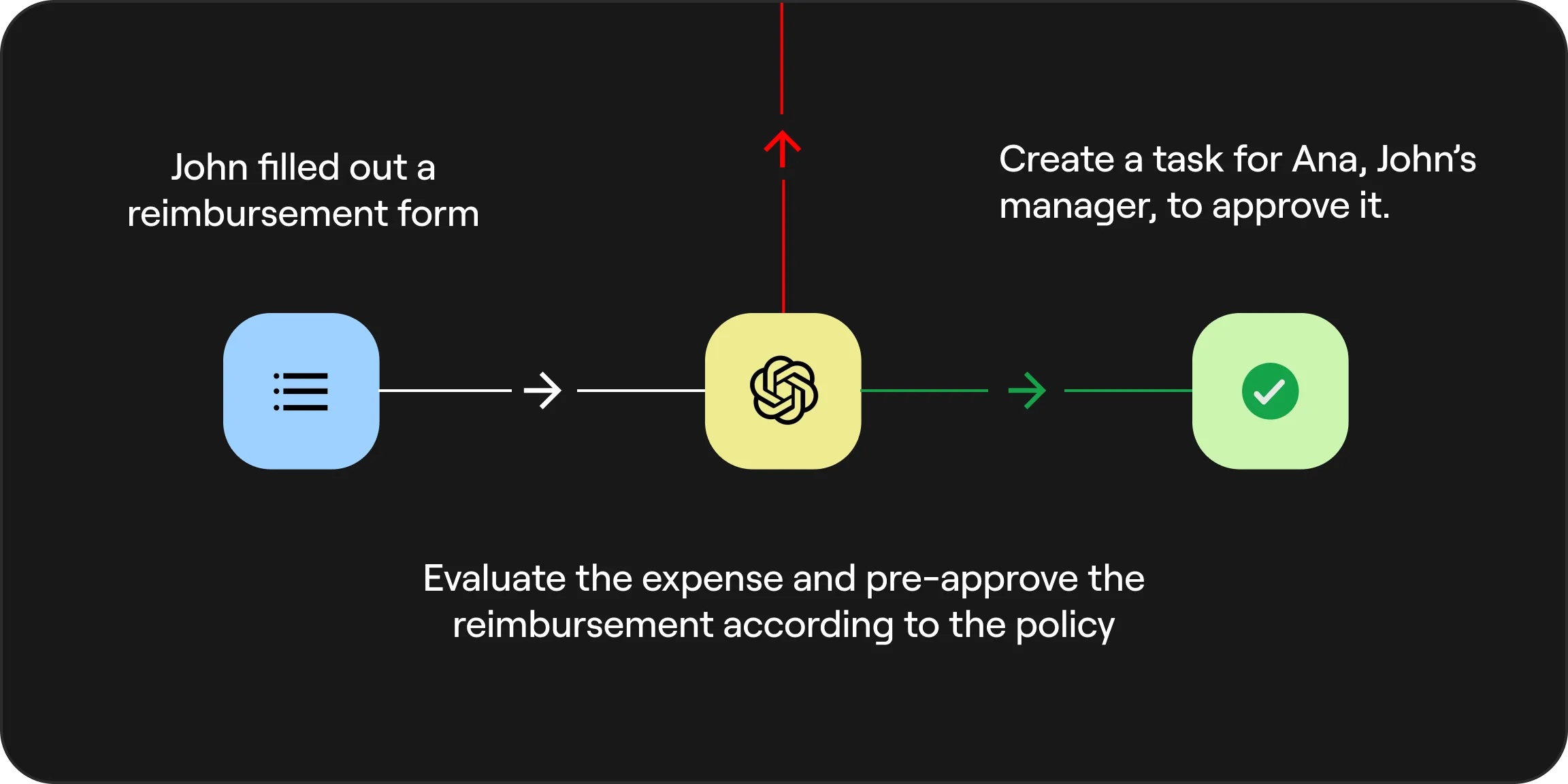
Process Automation (BPA): Replace manual work
Powerful Security and Flexible Permission Settings
What do the customers say?
"19 spreadsheets replaced — now turned into standardized workflows with all the control and security that Jestor offers."
"Jestor helped us replace manual work that was previously done using spreadsheets, Google Docs, WhatsApp, and Pipefy."